After todays app update, Kite asks to enable 2FA Security…
App based TOTP is already enabled for my account and it works fine.
Then why ask users to enable Biometric Device Lock/Verification?
This Support Artiicle (article needs editing to be unambiguous) says TOTP ‘OR’ Device Lock, I am already using TOTP, then enabling device lock will still be mandatory?
The Google itself clarified that Biometrics are less secure than strong PIN or Password.
What happens if Android User is not using Fingerprint Lock or Face Lock and instead he is using Password/PIN based Device Lock? In this case how does the whole process is implement/executed?
Is this feature is something similar to what many apps like Mozilla Lockwise or Firefox implements for unlocking stored Passwords where instead asking Android User to set new PIN/Password to unlock the app or app data, already set android device lock PIN/Password is used?
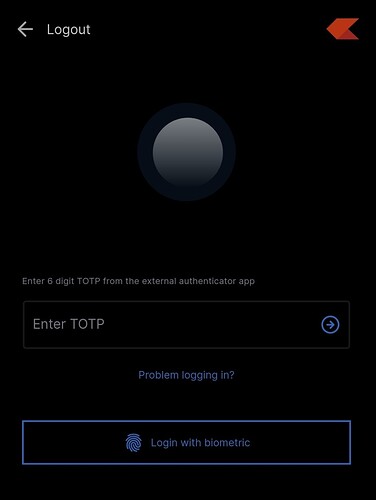
What happens to TOTP which Kite app asks (before this biometric 2FA updated) every time on opening the app? After enabling this Device Lock as 2FA, will TOTP still be required to Login into Kite app or the app can be unlocked with Fingerprint alone? (again is it going to just fingerprint OR fingerprint + PIN OR just Device Unlocking PIN/Password will be sufficient)?
Won’t this biometric thing be LESS SECURE as compared to KITE App login on a device which is protected with [Strong PIN/Password + TOTP 2FA app protected with different Strong PIN/Password + TOTP to unlock Kite app]?
If device unlock accepts Android device unlock PIN and use ONLY that without combining that with TOTP, then how is it different from earlier PIN based login mode used on Kite earlier, where user needed to enter password and then 6-digit fixed PIN [this login scheme is now defunct (AFAIK) after TOTP was made mandatory].
There are many questions like above, I hope you will post something on Z-Connect considering all possible scenarios to clarify on this device (un)lock 2FA.
There are many devices with different device unlock methods like PIN, Pattern, Password, Biometric, Face ID etc. Which of these will be accepted for device unlock mode to unlock Kite?
The NSE Notification which also allowed non-biometric authentication for cases where biometric authentication is not possible, how Zerodha is going to implement this?
@nithin @ShubhS9